南昌it培训机构排名前十
为大家整理的关于“南昌it培训机构排名前十”的相关信息。相信在IT领域发展的同学对Java很熟悉。Java编程语言排行中一直处于领先地位,这可以直接体现Java的重要。因此很多同学准备参加Java培训机构系统学习。那么,Java培训机构哪家比较好?下面我们介绍一下。

java一直是IT行业的高薪代表,其功能强大,简单易用,如今也是全球范围内使用人数比较多的编程语言之一,基于其强大的发展前景,java目前仍然十分火热,去专业的java培训学校进行学习,这也是快速入门的学习方式。国内java培训学校哪家好?小编带大家了解一下南昌it培训机构排名前十:
1、火星时代-快速从小白到大神
2、汇众教育-专注游戏开发培训/动漫设计培训/影视后期剪辑
3、达内教育-IT培训/UI设计/运营/影视特效培训机构
4、中公IT教育培训机构-编程培训
5、天琥教育-专注互联网视觉教育
6、千锋教育培训
7、博为峰培训-零基础学博为峰
8、东方瑞通
9、美迪电商教育
10、新猿教育-IT教育培训机构
以上排名不分先后,仅供参考。
C/C++代码安全漏洞审计,你知道多少?
代码审计,大家估计见到最多的一般是web程序的代码审计。然而c/c++这种语言的代码审计估计就很少了。
今天我们要来学习一下,工欲善其事必先利其器,今天介绍一款审计的利器Flawfinder(当然同类的还有很多工具,比如
RATS,RIPS,VCG,Fortify SCA,GOLD,YASCA等等)。该工具我搭建运行在ubuntu16.0.4LTS系统之上。
Flawfinder是一个C/C++代码的开源安全审查工具,采用内建语法缺陷数据库,能够标记类似缓冲溢出、格式字符串、竞争条件、随
机数获取方面的问题。Flawfinder是一个非常简单的工具,采用的算法也不复杂,可以看做是一个基于词典的源代码静态分析器。
Flawfinder的开发者David Wheeler表示:很多软件开发者都在不断重复犯相同的错误,开发人员应当在软件部署前就
用Flawfinder审查代码。 官方地址#/flawfinder/
0x02 flawfinder
root@ubuntu:~/Desktop# flawfinder --h
*** getopt error: option --h not a unique prefix
flawfinder [--help | -h] [--version] [--listrules]
[--allowlink] [--followdotdir] [--nolink]
[--patch filename | -P filename]
[--inputs | -I] [--minlevel X | -m X]
[--falsepositive | -F] [--neverignore | -n]
[--context | -c] [--columns | -C] [--dataonly | -D]
[--html | -H] [--immediate | -i] [--singleline | -S]
[--omittime] [--quiet | -Q]
[--loadhitlist F] [--savehitlist F] [--diffhitlist F]
[--] [source code file or source root directory]+
The options cover various aspects of flawfinder as follows.
Documentation:
--help | -h Show this usage help.
--version Show version number.
--listrules List the rules in the ruleset (rule database).
Selecting Input Data:
--allowlink Allow symbolic links.
--followdotdir
Follow directories whose names begin with ".".
Normally they are ignored.
--nolink Skip symbolic links (ignored).
--patch F | -P F
Display information related to the patch F
(patch must be already applied).
Selecting Hits to Display:
--inputs | -I
Show only functions that obtain data from outside the program;
this also sets minlevel to 0.
-m X | --minlevel=X
Set minimum risk level to X for inclusion in hitlist. This
can be from 0 (``no risk'') to 5 (``maximum risk''); the
default is 1.
--falsepositive | -F
Do not include hits that are likely to be false positives.
Currently, this means that function names are ignored if
they're not followed by "(", and that declarations of char-
acter arrays aren't noted. Thus, if you have use a vari-
able named "access" everywhere, this will eliminate refer-
ences to this ordinary variable. This isn't the default,
because this also increases the likelihood of missing
important hits; in particular, function names in #define
clauses and calls through function pointers will be missed.
--neverignore | -n
Never ignore security issues, even if they have an ``ignore''
directive in a comment.
--regex PATTERN | -e PATTERN
Only report hits that match the regular expression PATTERN.
Selecting Output Format:
--columns | -C
Show the column number (as well as the file name and
line number) of each hit; this is shown after the line number
by adding a colon and the column number in the line (the first
character in a line is column number 1).
--context | -c
Show context (the line having the "hit"/potential flaw)
--dataonly | -D
Don't display the headers and footers of the analysis;
use this along with --quiet to get just the results.
--html | -H
Display as HTML output.
--immediate | -i
Immediately display hits (don't just wait until the end).
--singleline | -S
Single-line output.
--omittime Omit time to run.
--quiet | -Q
Don't display status information (i.e., which files are being
examined) while the analysis is going on.
Hitlist Management:
--savehitlist=F
Save all hits (the "hitlist") to F.
--loadhitlist=F
Load hits from F instead of analyzing source programs.
--diffhitlist=F
Show only hits (loaded or analyzed) not in F.
For more information, please consult the manpage or available
documentation.
0x03 示例
代码
命令
copy
flawfinder --columns --context main.c --html
也可以保存成文档
copy
flawfinder --columns --context main.c --html result.html
0x04 结果分析
copy
Flawfinder version 1.31, (C) 2001-2014 David A. Wheeler.
Number of rules (primarily dangerous function names) in C/C++ ruleset: 169
Examining main.c
Warning: Skipping non-existent file --html
FINAL RESULTS:
main.c:7:2: [5] (buffer) gets:
Does not check for buffer overflows (CWE-120, CWE-20). Use fgets() instead.
gets(ch,stdin);
main.c:6:2: [2] (buffer) char:
Statically-sized arrays can be improperly restricted, leading to potential
overflows or other issues (CWE-119:CWE-120). Perform bounds checking, use
functions that limit length, or ensure that the size is larger than the
maximum possible length.
char ch[50];
ANALYSIS SUMMARY:
Hits = 2
Lines analyzed = 9 in approximately 0.01 seconds (1170 lines/second)
Physical Source Lines of Code (SLOC) = 9
Hits@level = [0] 0 [1] 0 [2] 1 [3] 0 [4] 0 [5] 1
Hits@level+ = [0+] 2 [1+] 2 [2+] 2 [3+] 1 [4+] 1 [5+] 1
Hits/KSLOC@level+ = [0+] 222.222 [1+] 222.222 [2+] 222.222 [3+] 111.111 [4+] 111.111 [5+] 111.111
Minimum risk level = 1
Not every hit is necessarily a security vulnerability.
There may be other security vulnerabilities; review your code!
See 'Secure Programming for Linux and Unix HOWTO'
(#/secure-programs) for more information.
main.c:7:2: [5] (buffer) gets: //第七行 没有检查buffer缓存会溢出。
Does not check for buffer overflows (CWE-120, CWE-20). Use fgets() instead.
gets(ch,stdin);
main.c:6:2: [2] (buffer) char: //第六行 静态分配的数组大小会被溢出。
Statically-sized arrays can be improperly restricted, leading to potential
overflows or other issues (CWE-119:CWE-120). Perform bounds checking, use
functions that limit length, or ensure that the size is larger than the
maximum possible length.
char ch[50];
ANALYSIS SUMMARY: //分析总结
Hits = 2 //两个可疑点
Lines analyzed = 9 in approximately 0.01 seconds (1170 lines/second) //总共9行代码用时0.01s
Physical Source Lines of Code (SLOC) = 9
Hits@level = [0] 0 [1] 0 [2] 1 [3] 0 [4] 0 [5] 1
Hits@level+ = [0+] 2 [1+] 2 [2+] 2 [3+] 1 [4+] 1 [5+] 1
Hits/KSLOC@level+ = [0+] 222.222 [1+] 222.222 [2+] 222.222 [3+] 111.111 [4+] 111.111 [5+] 111.111
Minimum risk level = 1
Not every hit is necessarily a security vulnerability. //注意此处,不是所有的可疑点都是安全漏洞
There may be other security vulnerabilities; review your code!
See 'Secure Programming for Linux and Unix HOWTO'
(#/secure-programs) for more information.
0x05 总结
自动化的静态代码审计工具虽然可以在某种程度节省代码审计的人力成本,时间成本。
是提高代码审计效率的重要手段。然而需要注意的是,自动化工具并非是完全智能准确的,
跟所有的检测扫描工具一样,误报率的存在仍然是必须面对的现实问题。因此,检测结果
中显示的漏洞还是需要审计人员,手动验证或者手工进一步确认是否真的存在。
版权说明:本篇文章转载于百度搜索,只用于学习与交流。
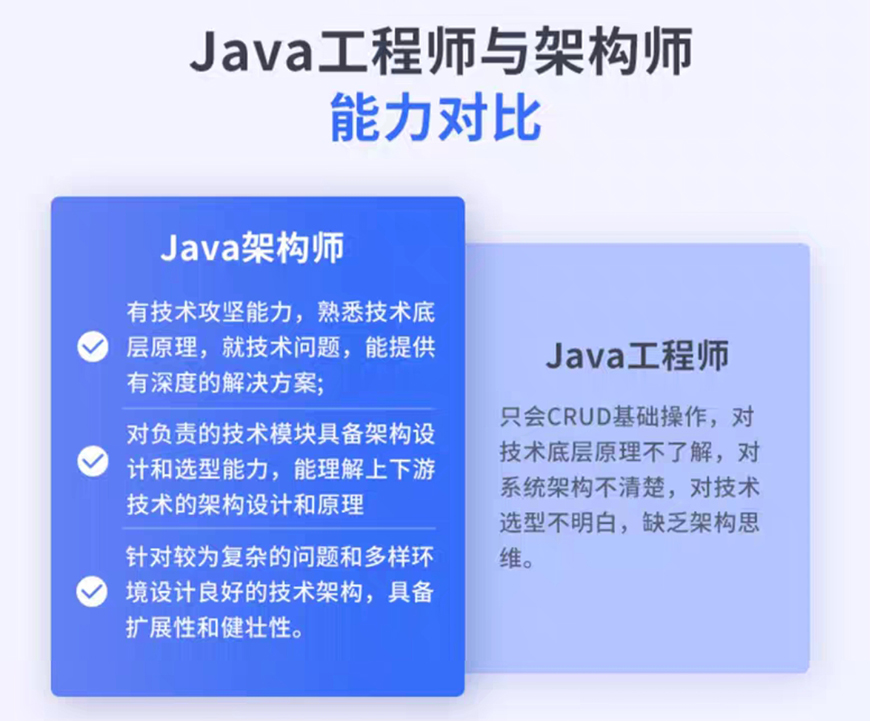
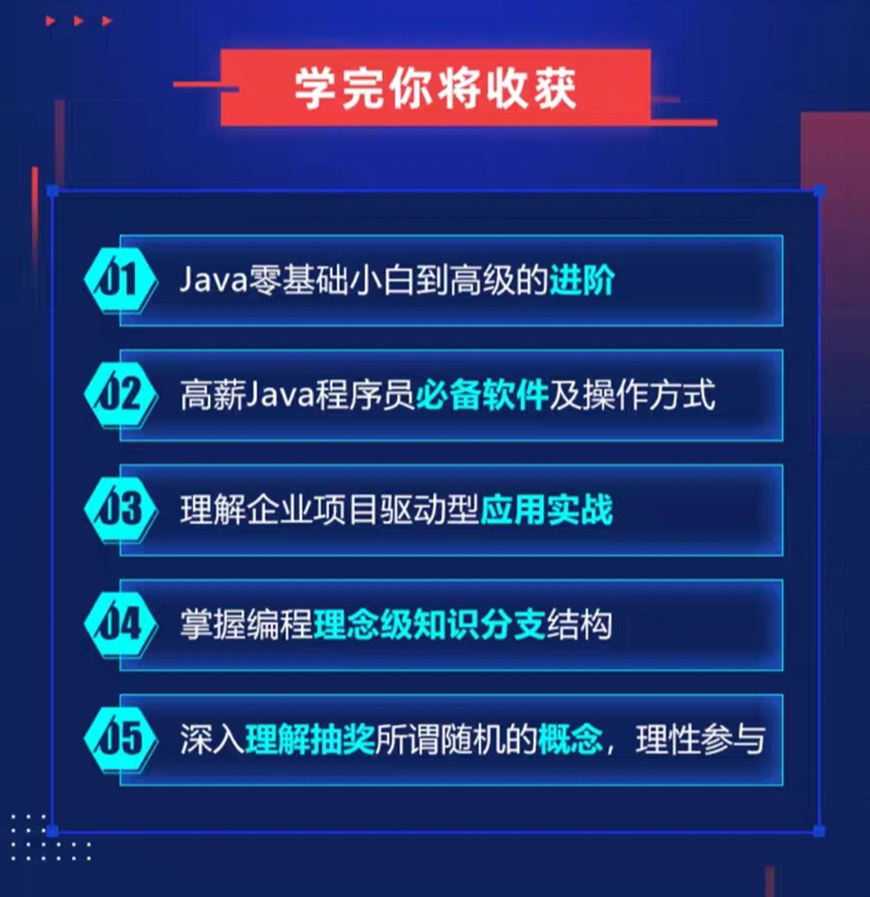
java工程师应该具备以下的一些实际技能:一、强化java基础。目前java的新技术层出不穷,各企业各有侧重,根据企业用人需求,只有具备扎实java基础的程序员才能掌握新技术。对核心算法、面向对象应用、数据结合与集合框架、反射、输入输出、多线程、异常处理等都有深入的研究。二、熟悉linux操作系统的使用。今天,linux被用作广泛的服务器操作系统。有资格的java工程师必须具有linux操作技能,这也是企业面试中加分的一个重要指标。三、深入学习数据库技术。因特网公司没有数据库技术就无法应用于java。无论哪种大中型应用,数据库设计的优劣、数据库访问的效率直接决定工程的成败。目前数据库主流技术有oracle和mysql两种,除了熟练地应用数据库架构和sql语句外,还需要掌握数据库设计、sql语句优化等方面的知识。四、网络前端系统技术。由于因特网技术从web2.0发展到web3.0,web前端技术,包括html,css,尤其是javascript,越来越受到企业界的关注。许多公司为此设立了“web前端工程师”的职位,所以作为一个合格的java工程师,要不断地学习java知识,包javascript,以及相关的ajax,jquery框架,ext-js框架。五、机构和框架。javascript是一个组件和框架的世界,所有的java程序员都应该了解java框架。六、专门的企业级开发和部署环境企业界需要特定的软件环境来进行开发、测试和部署实际项目,但许多技术人员往往对此不太重视,因此在工作中会出现许多问题和错误,甚至被淘汰出局。作为java工程师,您应该知道一些关于linux命令集脚本编程,远程登录,art,单元测试技术,maven构建技术,svn应用技术的知识。七、规范的企业发展过程和文件资料。软体开发是一个团队的工作,所以企业的开发过程和文件说明尤其重要。它也是区分“基层程序员”和“普通程序员”的一个重要标志。发展项目不论规模大小,都应遵循企业开发的过程(需求分析,系统设计,代码实现,单元测试,系统测试,部署上线)。


以上是关于“南昌it培训机构排名前十”的相关资讯,希望对您有所帮助,正规Java工程师培训机构选择达内教育就是选择了花钱少、学习真正的技能,早学习早受益,更多的关于Java工程师培训费用以及校区地址问题,请咨询在线客服。
更多培训课程,学习资讯,课程优惠,课程开班,学校地址等学校信息,请进入
教育新闻
详细了解
你也可以留下你的联系方式,让课程老师跟你详细解答: 在线咨询